Hackers need ways to install malware on your computer. They use email, shady executable files and Internet web pages. A drive-by download is one method that uses the Internet and web pages to install malicious software on your computer. Drive-by software can be installed several ways on your computer, but you can avoid having viruses and keyloggers installed on your machine if you’re aware of common tricks.
The Drive-By Trick
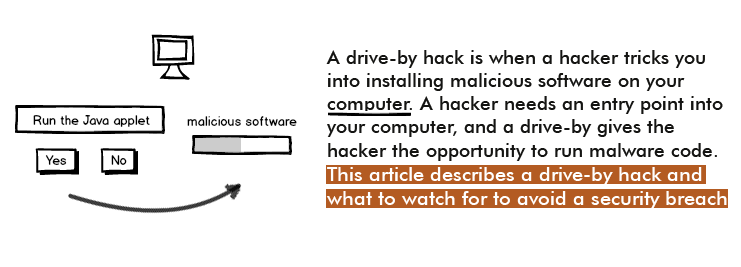
Malware creators use methods that trick users into installing viruses and keyloggers using common web browser tricks. When web browsers need to run Java or custom software, the browser asks for permission to run the application. Web developers can create custom applications using Java or old Microsoft ActiveX scripts. ActiveX is not popular anymore, but Java applets are still a part of some web pages. Giving permission to these custom applications means you give permission for an executable to run on your local computer.
When you land on a web page that uses a Java app, you’re asked to install Java or run the applet. When you run Java through the Internet, the code runs on your local computer.
Running apps on your computer is the trick to a drive-by hack.
Most users don’t analyze the type of site that wants to run a Java applet, and it’s a mistake to run just any generic applet on your computer. However, users approve permission and the Java applet runs. The common web browsers (Internet Explorer, Firefox and Chrome) ask permission before allowing these apps to run. Users give permission to these sites, and the result can be a devastating effect on your computer’s security.
What Can Happen if You Run a Drive-By on Your Computer
Java runs directly on your computer, so the application can perform almost any activity as it executes. The common effect from a drive-by install is a keylogger installation. While most antivirus software applications detect keyloggers, antivirus software does not always detect new keyloggers created by new hacks in the wild. The effect of a keylogger is all your keystrokes are logged and sent to a hacker. This means that your passwords, account numbers and login information are sent to a hacker. All of your private information is at risk when you run a keylogger on your computer.
How You Can Defend Against a Drive-By Installation
The first defense is common sense. If a strange website is asking to run software on your computer, deny permission to your computer. Any reputable browser will then block the application, and your computer is safe from the malware.
If you accidentally give permissions to malware programs, you can add some security by always running antivirus software while browsing the Internet. Even if you accidentally run malware programs, an antivirus program will intercept the software execution and stop the application from running on your computer. You receive an alert from your antivirus software, and the application is quarantined where you can delete it later.
Another option is firewall software. Firewalls block access to specific ports, which includes the port that connects to the Internet. When a drive-by application attempts to upload information to a hacker’s site, the firewall gives you an alert and blocks the transmission.
Malware can ruin your privacy and leave you stuck with a crashed computer. Use some common sense when running applets on your computer, but always keep antivirus and firewall software running on your machine for extra protection.
