In early 2015, Lenovo released a statement to its customers about SuperFish, a piece of software that came preinstalled with some laptop and notebook computers. For over half a year, the adware had been on users’ computers, and while Lenovo thought it was helpful, SuperFish actually used fake SSL encryption and other methods that left users vulnerable to ads and, even worse, hackers.
You could tell if your system was infected because pages would show price comparisons when looking at products and services. The message that this was powered by “VisualDiscovery” would show up, but there was no sign of the word “SuperFish” anywhere around. In fact, price comparison “tools” are a common type of adware. One third-party tool that was designed to detect the presence of SuperFish on computers would even try to trigger the popups created by the adware.
Lenovo also released a tool to completely remove SuperFish, even if it wasn’t listed as a program installed on the PC, after receiving complaints from users. While there was no official number of infected systems released, a number of devices, including those in the Y, U, and YOGA series, were susceptible. Although Lenovo may have acted swiftly, some people were critical of the company for including the third-party software, which was completely unnecessary, on their machines in the first place.
How Adware Works
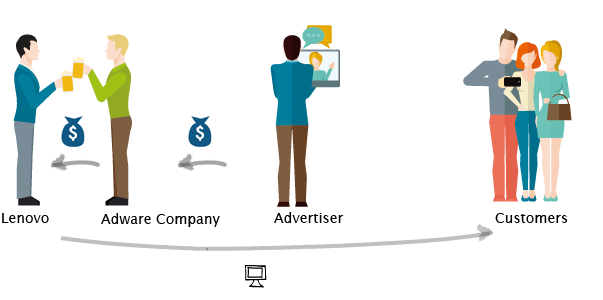
This is nothing new for adware companies, which have been hitching a ride with legitimate software for years. They pay creators of software to be included, betting that users won’t pay attention. The last time you installed a Java update on your computer, for example, you had the option to install browser plugins from Ask.com. Of course, no one actually uses Ask.com, but you’ll find the toolbar and possibly changes to your search engine and home pages if you don’t carefully read the options when installing Java, which is necessary to load some apps.
SuperFish’s bet paid off. Users didn’t realize the program was on their PCs, and they were able to load ads and make even more money from those systems. Because adware is lucrative, both for the creators of the adware and the companies making a quick but by including it with their install, it’s unlikely that the practice will disappear anytime soon. This is why users must be so vigilant when installing software or even downloading files from the Internet.
Conclusion
It’s going to be a lot more difficult to locate potential issues like SuperFish if you don’t know what to look for when you buy a new computer. In fact, some users who had remnants of this particular piece of adware on their systems even when there was no listing of the program in the control panel. Lenovo’s SuperFish removal tool looked for registry values and other files associated with Superfish to remove them. Trades of this software may even exist on your machine even if the program itself didn’t.
What may even more disturbing about SuperFish is how the software used an SSL certificate. Typically, you know you can trust a website when it loaded using SSL — your browser will show an address starting with “https” and an icon indicating the site uses SSL. SuperFish relied on the trust that users had in SSL, a trust that should be well-placed. Because of this, many users disabled the SSL certificate used by SuperFish. However, Microsoft also updated Windows Defender to disable the faulty certificate.
There’s a lot to be learned from the SuperFish incident. PC users can no longer blindly rely on a website’s SSL status, and they should keep an eye out for the common traits of adware. Price comparison popups are one of many. However, it really falls onto companies like Lenovo to look beyond the bottom line of padding their pockets and protect their users from nasty adware like SuperFish. An incident like this could easily damage a company’s reputation and irrevocably break trust with consumers.
